Artikel ini akan memberi tahu Anda tentang sistem pemantauan Zabbix dan eksperimen di mana serangan akan dilakukan pada sistem operasi dengan agen yang sudah diinstal sebelumnya. Percobaan akan mencakup skenario - eksploitasi kerentanan Zerologon.
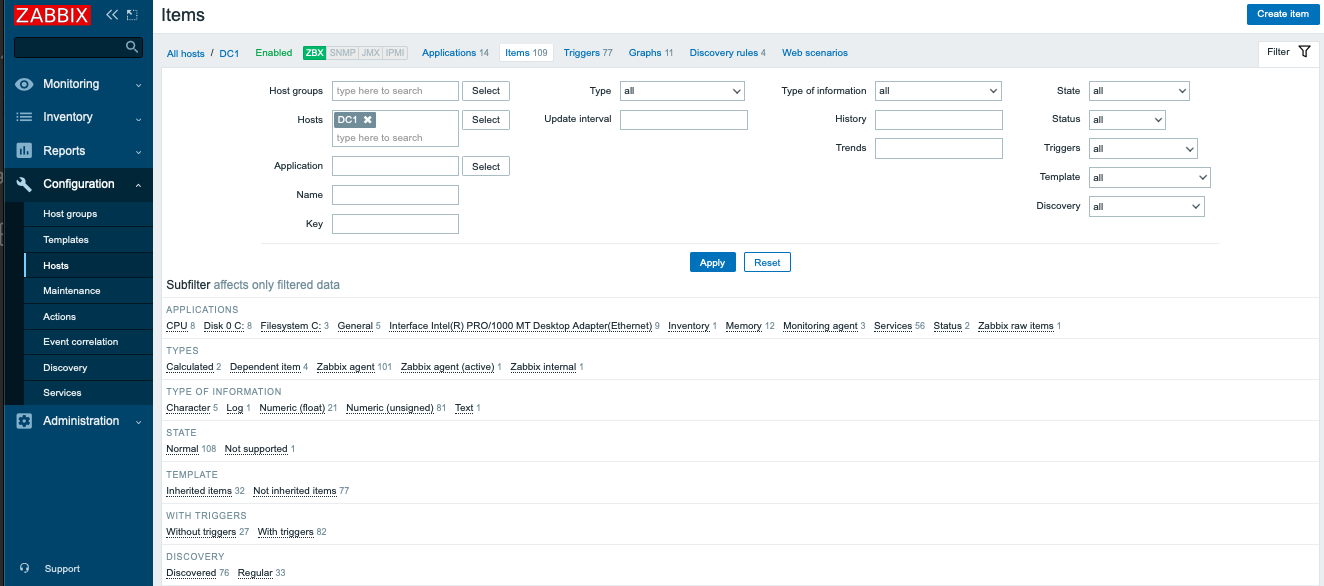
Konsep dasar Zabbix
Zabbix . . Zabbix . , Zabbix .
Zabbix, - -, , , .
Zabbix . . : "zabbix CVE inurl:exploit-db"
.
2 :
Ubuntu 20.04 ;
Windows Server 2019 ( Zerologon)
. Ubuntu Windows . . , . , , :

Windows , . .
RCE
Zabbix, , , . , , .
.
CVE-2020-1472
NetLogon. , . , . 1 255 . . 10 40 . ?
Windows . , . , "Security". , . / , . , , , , . MSDN, :
5827 - NetLogon . ;
5828, 5829 - , NetLogon.
, . , .
Zabbix , :
<?xml version="1.0" encoding="UTF-8"?>
<zabbix_export>
<version>4.4</version>
<date>2020-09-16T02:47:03Z</date>
<groups>
<group>
<name>Domain Controllers</name>
</group>
</groups>
<templates>
<template>
<template>Netlogon Elevation of Privilege Vulnerability - CVE-2020-1472</template>
<name>Netlogon Elevation of Privilege Vulnerability - CVE-2020-1472</name>
<description>Monitors event ID's 5827, 5828 & 5829 for CVE-2020-1472
https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2020-1472</description>
<groups>
<group>
<name>Domain Controllers</name>
</group>
</groups>
<applications>
<application>
<name>Event Log</name>
</application>
</applications>
<items>
<item>
<name>Event ID: 5827 - Vulnerable Netlogon secure channel connection (CVE-2020-1472)</name>
<type>ZABBIX_ACTIVE</type>
<key>eventlog[System,,,,5827]</key>
<trends>0</trends>
<value_type>LOG</value_type>
<description>See Step 2b: Addressing event IDs 5827 and 5828
https://support.microsoft.com/en-au/help/4557222/how-to-manage-the-changes-in-netlogon-secure-channel-connections-assoc</description>
<applications>
<application>
<name>Event Log</name>
</application>
</applications>
<triggers>
<trigger>
<expression>{nodata(180)}=0</expression>
<name>Event ID: 5827 - Vulnerable Netlogon secure channel connection (CVE-2020-1472)</name>
<priority>HIGH</priority>
<description>See Step 2b: Addressing event IDs 5827 and 5828
https://support.microsoft.com/en-au/help/4557222/how-to-manage-the-changes-in-netlogon-secure-channel-connections-assoc</description>
</trigger>
</triggers>
</item>
<item>
<name>Event ID: 5828 - Vulnerable Netlogon secure channel connection (CVE-2020-1472)</name>
<type>ZABBIX_ACTIVE</type>
<key>eventlog[System,,,,5828]</key>
<trends>0</trends>
<value_type>LOG</value_type>
<description>See Step 2b: Addressing event IDs 5827 and 5828
https://support.microsoft.com/en-au/help/4557222/how-to-manage-the-changes-in-netlogon-secure-channel-connections-assoc</description>
<applications>
<application>
<name>Event Log</name>
</application>
</applications>
<triggers>
<trigger>
<expression>{nodata(180)}=0</expression>
<name>Event ID: 5828 - Vulnerable Netlogon secure channel connection (CVE-2020-1472)</name>
<priority>HIGH</priority>
<description>See Step 2b: Addressing event IDs 5827 and 5828
https://support.microsoft.com/en-au/help/4557222/how-to-manage-the-changes-in-netlogon-secure-channel-connections-assoc</description>
</trigger>
</triggers>
</item>
<item>
<name>Event ID: 5829 - Non-compliant device event has been generated (CVE-2020-1472)</name>
<type>ZABBIX_ACTIVE</type>
<key>eventlog[System,,,,5829]</key>
<trends>0</trends>
<value_type>LOG</value_type>
<description>See section: Addressing event 5829
https://support.microsoft.com/en-au/help/4557222/how-to-manage-the-changes-in-netlogon-secure-channel-connections-assoc</description>
<applications>
<application>
<name>Event Log</name>
</application>
</applications>
<triggers>
<trigger>
<expression>{nodata(180)}=0</expression>
<name>Event ID: 5829 - Non-compliant device event has been generated (CVE-2020-1472)</name>
<priority>HIGH</priority>
<description>See section: Addressing event 5829
https://support.microsoft.com/en-au/help/4557222/how-to-manage-the-changes-in-netlogon-secure-channel-connections-assoc</description>
</trigger>
</triggers>
</item>
</items>
</template>
</templates>
</zabbix_export>
, , :
, , . .
OTUS " : Zabbix, Prometheus, ELK". 15 .